Digital identity verification is now essential for securing international trade. Fraud in cross-border transactions is rising, with global payment volumes reaching $1 quadrillion in 2024 and criminals exploiting gaps in KYC (Know Your Customer) and AML (Anti-Money Laundering) processes. The stakes are high – businesses lose billions annually to scams like synthetic identity fraud, Business Email Compromise (BEC), and trade-based money laundering (TBML).
Key takeaways:
- Fraud Costs: $40 billion lost annually to international trade fraud, with recovery rates below 5% for cross-border scams.
- Verification Methods: Legal Entity Identifiers (LEIs), biometric checks with liveness detection, document verification using AI, and behavioral analysis are effective tools.
- Challenges: Regulatory inconsistencies, weak global KYC enforcement, and data privacy laws complicate verification.
- Solutions: Combining digital identity verification with Accounts Receivable Insurance (ARI) protects businesses from fraud and payment defaults.
For businesses, adopting layered verification methods and risk-based strategies is critical. These tools not only prevent fraud but also ensure compliance and financial stability in international markets.
Webinar: Trends in Digital Identity Management for Cross-Border Paperless Trade
sbb-itb-2d170b0
Fraud Risks in Cross-Border Transactions
International Trade Fraud Statistics and Financial Impact 2024-2025
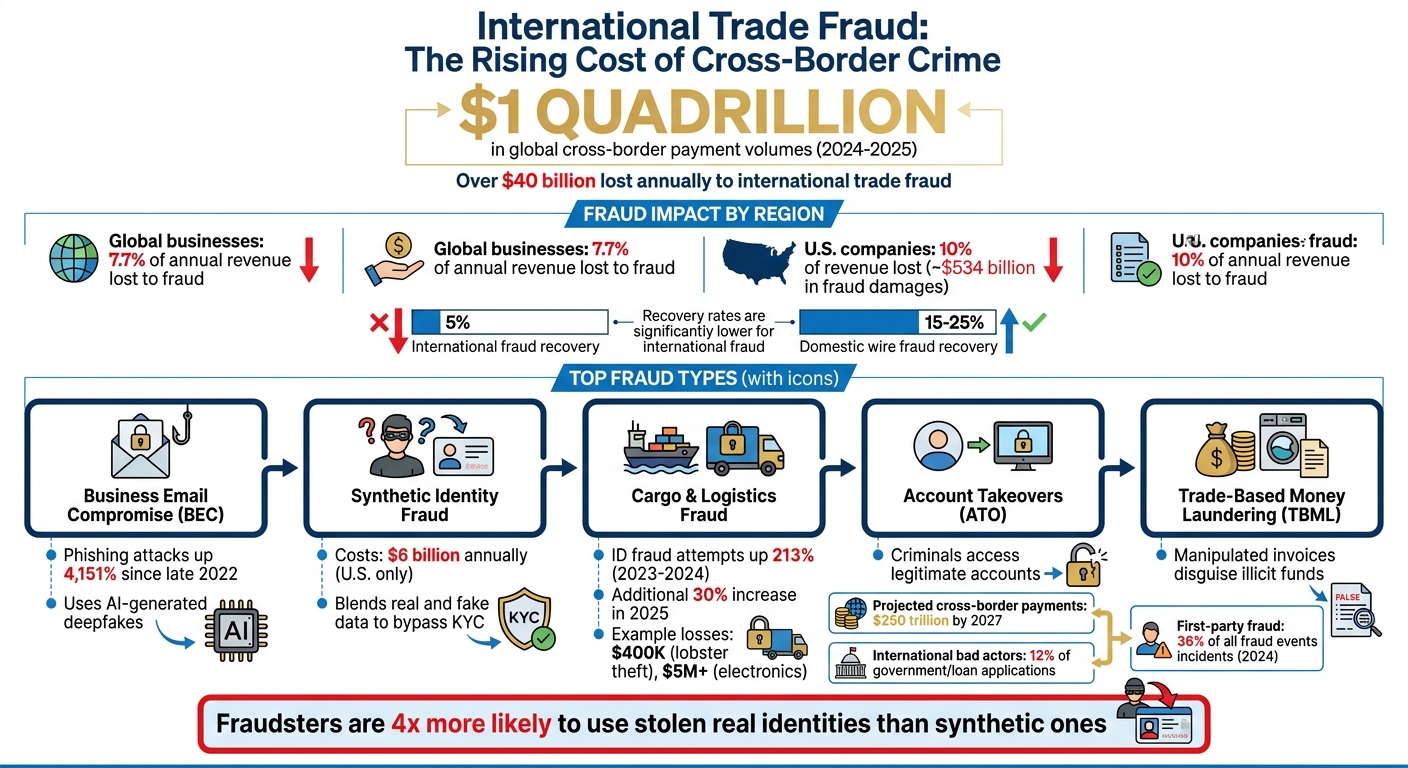
Cross-border transactions are a prime target for fraud. By 2025, global cross-border payment volumes are expected to hit a staggering $1 quadrillion, with criminals siphoning off over $40 billion annually through various schemes. On average, global businesses lose 7.7% of their annual revenue to fraud, while U.S. companies face even higher losses, nearing 10%, amounting to an estimated $534 billion in fraud-related damages.
The issue goes beyond sheer volume – it’s about systemic vulnerabilities. Brahim Oubrik of IdealRemit explains:
"International payments are disproportionately targeted for a simple reason: they are harder to unwind."
Recovering funds lost to domestic wire fraud is challenging enough, with only 15–25% being recovered. For international fraud, that figure drops below 5%. Once money crosses borders, it’s often funneled through intermediary accounts or converted to cryptocurrency, making recovery nearly impossible.
Common Fraud Scenarios in International Trade
Business Email Compromise (BEC) remains one of the most damaging fraud tactics. Scammers impersonate executives or suppliers to reroute payments overseas. With phishing attacks skyrocketing by 4,151% since late 2022 due to open-source AI tools, these scams have become increasingly sophisticated, even using AI-generated deepfakes to mimic executives.
Synthetic identity fraud is another growing issue, costing the U.S. over $6 billion annually. Fraudsters blend real and fake data to create identities that pass automated KYC checks. These identities, appearing legitimate in databases, are then used for cross-border transactions.
Cargo and logistics fraud has seen a sharp rise as well. ID fraud attempts in the logistics sector jumped 213% from 2023 to 2024, followed by another 30% increase in 2025. For example, one criminal group used fake IDs to steal $400,000 worth of lobster, while another orchestrated a theft of over $5 million in electronics using fraudulent credentials.
Other fraud types include account takeovers (ATO), where criminals access legitimate accounts to initiate unauthorized transfers, and triangulation fraud, which uses stolen payment details to buy goods that are then resold after being routed through unsuspecting intermediaries. Additionally, trade-based money laundering (TBML) manipulates invoices to disguise the movement of illicit funds.
Organized crime has gone global, offering "fraud-as-a-service" packages that include stolen credentials and synthetic identity kits. As Ira Bondar from Veriff puts it:
"For global scammers, borders are optional; for most businesses, they’re still blind spots."
These increasingly sophisticated methods make it harder for businesses to navigate the complexities of international regulations.
Regulatory Compliance Challenges
Inconsistent KYC and AML standards across countries create gaps that fraudsters exploit. They route funds through jurisdictions with lax onboarding rules or poor KYC enforcement into more regulated markets. This creates what experts call a "regulatory attack surface", where funds flow from high-regulation regions into low-friction digital accounts in areas with weak oversight.
Many compliance systems treat eKYC as a one-time checkpoint during onboarding, leading to an "Authorization Gap." As Ryu360, a specialist in digital forensics, explains:
"Successful authentication ≠ guaranteed control by the legitimate subject."
Fragmented compliance teams – separating AML, fraud, and KYC functions – further hinder real-time risk detection. Jennifer Pitt of Javelin Strategy & Research highlights:
"Because fraud and money laundering incidents increasingly overlap, failing to detect one can mean failing to detect the other. This is also why it’s critical that teams are not completely siloed."
Data protection laws also vary widely, complicating the verification of international counterparties. Poor-quality identity databases in certain regions and language barriers add to the challenge, particularly when verifying local names and addresses. Moreover, the U.S. lacks an Authorized Push Payment (APP) fraud reimbursement mandate, leaving victims to absorb their losses – unlike the UK, where reimbursement became mandatory in October 2024.
Ira Bondar sums up the situation:
"Fraudsters follow the path of least resistance: weak KYC in one country, lax enforcement in another, and slow information-sharing everywhere."
With 79% of U.S. organizations reporting attempted or actual payments-fraud incidents in 2024 and cross-border payment volumes expected to reach $250 trillion by 2027, businesses must prioritize advanced verification systems to keep up with evolving threats in international trade.
Digital Identity Verification Techniques
As fraud tactics become more sophisticated, businesses must adopt robust verification methods to safeguard cross-border transactions. By leveraging the right mix of technologies, companies can address vulnerabilities that criminals exploit when transferring money internationally. Here’s a closer look at some of the most effective techniques.
Legal Entity Identifier (LEI) and Verifiable LEI (vLEI)
The Legal Entity Identifier (LEI), based on the ISO 17442 standard, assigns a unique 20-character code to businesses involved in global transactions. Currently, more than 2.7 million businesses use an LEI, and over 200 financial regulators worldwide rely on it for business-to-government processes. The LEI helps answer critical questions like "who is who" and "who owns whom", which is essential when up to 42 different parties might need identification during a single trade lifecycle.
Building on this, the Verifiable LEI (vLEI) – standardized under ISO 17442-3 – introduces cryptographic verification. While the LEI identifies organizations, the vLEI goes further by confirming the authority of individuals acting on behalf of those organizations. David Campos, Head of Partnerships at GLEIF, highlights its significance:
"The LEI ensures global consistency of entity identification, while the vLEI enables cryptographic verification of that identity and associated authority in digital workflows."
This "verify once, use many" model allows businesses to reuse verified credentials across platforms and jurisdictions, cutting down on repetitive onboarding and manual KYC/AML checks. The vLEI is particularly impactful in Electronic Transferable Records (ETRs), such as digital bills of lading and promissory notes. By digitally signing these documents with vLEI credentials, companies create clear audit trails and minimize the risk of fraudulent activity. Darragh Hayes, CEO of LEI Worldwide, explains the shift:
"The LEI is no longer just a financial identifier – it’s becoming a passport for participation in the digital trade ecosystem."
Biometric Authentication
Adding a human element to verification, biometric authentication uses physical traits like fingerprints, facial recognition, and retina scans to confirm individual identities. These unique characteristics are incredibly difficult to replicate, making biometric methods more secure than traditional passwords or documents. However, with generative AI now playing a role in 85% of identity fraud cases, biometric systems must incorporate liveness detection to verify that a real person is present during authentication.
Liveness detection protects against fraudsters using photos, videos, or AI-generated deepfakes to bypass systems. Platforms like Plaid have achieved pass rates of 90% or higher, while significantly reducing fraud, by combining biometric checks with liveness detection. This layered approach is critical as first-party fraud has surged, now accounting for 36% of all fraud events, and biometric verification is particularly effective at preventing account takeovers and the misuse of stolen identities. Fraudsters are approximately 4 times more likely to use stolen real identities than synthetic ones. For government services and international loans, this is especially relevant, as international bad actors are responsible for up to 12% of incoming applications.
Document and Data Verification
Document verification employs Optical Character Recognition (OCR) and AI to instantly authenticate trade documents. Edmund Ng, Regional Sales Director at Melissa, explains the dual advantage:
"AI can spot suspicious behaviors and inconsistencies by analyzing a large amount of data quickly. OCR, on the other hand, can conduct real-time document scanning and verification."
This method cross-references documents with global databases to confirm identities. When paired with the vLEI, document verification becomes even more powerful. David Campos of GLEIF notes:
"The vLEI extends the LEI into digitally signed, tamper-evident credentials… This supports higher assurance and automation while preserving clear accountability."
With cross-border payments projected to reach $1 quadrillion in 2024, automated document verification is essential for reducing manual errors and speeding up processing. Businesses can integrate verification into their systems via APIs, avoiding manual workarounds that may introduce vulnerabilities. To enhance accuracy, these systems should adapt to the regulatory and data requirements of different countries. Behavioral and device data can further complement document checks, adding another layer of security.
Behavioral and Device-Based Analysis
Behavioral analysis observes user interactions – like typing speed, navigation patterns, and mouse movements – to differentiate between legitimate users and potential fraudsters. Device and IP intelligence adds another dimension by examining factors such as IP geolocation, VPN usage, and time zone inconsistencies to flag high-risk activities.
Modern systems can detect suspicious patterns, such as multiple identity sessions originating from the same device in a short period – a common sign of coordinated fraud. This is especially valuable for transaction monitoring, which identifies unusual behavior, as opposed to screening, which focuses on connections to restricted parties or regions.
To enhance accuracy and minimize false positives, businesses should combine behavioral data with contextual attributes like birth dates, company registration numbers, and vessel identifiers. This multi-layered strategy makes it significantly harder for fraudsters to bypass verification systems. Toomas Pavelson of LEI Register underscores the importance of precise identification:
"In the digital economy… when something goes wrong, such as a cyber-attack or system outage, organisations need to know immediately which partners are involved and how those risks affect their own operations."
Benefits and Trade-Offs of Digital Identity Verification
Digital identity verification offers clear security advantages for international trade but comes with its share of costs and operational hurdles. Weighing these factors is critical for businesses deciding how and when to implement such systems.
On the security front, the statistics speak volumes. Combining document verification with at least one biometric or database check can reduce identity fraud acceptance rates by a staggering 89% compared to single-method systems. For businesses engaged in cross-border transactions, this level of protection is crucial in combating threats like Business Email Compromise (BEC) attacks and synthetic identity fraud. In fact, 71% of business leaders view improved security and fraud prevention as the top benefits of integrating digital identity solutions.
Efficiency is another standout benefit. Seventy-four percent of business leaders highlight increased operational efficiency as a key advantage. Automated document verification, for example, can achieve OCR field extraction accuracy rates of 98.7% and a fraud detection recall of 94.8%. Scott Johnson, Vice President of Technical Program Management at Convera, underscores the need for digital verification in today’s fast-paced financial services environment:
"Generally speaking, financial services have gotten faster… But that doesn’t necessarily mean that compliance and KYC processes have kept up."
However, these benefits come with notable costs. For a company handling 50,000 checks annually, first-year ownership costs can range from $42,000 to $283,000. This includes per-check fees, integration costs, annual maintenance, and approximately $12 per false positive. Additionally, high-security methods like biometric liveness checks can introduce friction, potentially leading to higher abandonment rates during onboarding.
Regulatory complexity adds another layer of difficulty. Businesses must navigate conflicting international regulations like the EU’s GDPR and the U.S.’s CCPA, both of which impose strict requirements around data minimization and user consent. Adoption is also limited – fewer than 10% of businesses currently use digital identity schemes, which diminishes their overall utility. As Scott Johnson points out:
"If 10% of the population is using a digital identity scheme, probably no company is going to do the work to integrate with it. It won’t have utility, and then the remaining 90% of the population will not want to use it."
To better understand these trade-offs, let’s compare the pros and cons of common verification methods.
Comparison Table of Implementation Trade-Offs
| Method | Security Level | User Friction | Cost per Check | Best Use Case |
|---|---|---|---|---|
| Database Verification | Low/Medium | None | $0.10 – $0.80 | Low-risk retail, fast onboarding |
| Document (OCR) | High | Medium | $0.50 – $3.00 | AML/KYC compliance, B2B trade |
| Biometric Matching | Very High | Medium | +$0.30 – $1.50 | High-value transactions, anti-spoofing |
| Behavioral Analysis | Medium | None | $0.01 – $0.05 | Continuous monitoring, anti-takeover |
| Knowledge-Based (KBA) | Low | Low | Low | Obsolete for primary verification |
To get the most out of digital identity verification, businesses should adopt a risk-based approach. For lower-risk transactions, such as retail purchases, database checks are sufficient and cost-effective. For high-value activities like international trade or large contracts, combining document and biometric verification is a smarter choice. Before committing to a vendor, businesses should run a 30-day pilot involving at least 1,000 real-world verifications to assess actual performance in terms of accuracy, speed, and false positive rates.
Implementation Strategies for International Trade
Rolling out digital identity verification in international trade requires detailed planning and careful execution. Start by identifying the key areas where identity verification is critical – such as payment systems, payout partners, marketplaces, and onboarding processes that operate across borders. By mapping out these areas, you can uncover vulnerabilities where weak verification in one region might expose the entire operation to fraud.
Next, evaluate regional risks. Not all trade routes or regions carry the same level of risk. Group regions based on factors like historical fraud data, enforcement weaknesses, and the presence of known fraud networks. Apply stricter verification measures in higher-risk areas to mitigate potential threats.
A phased rollout is often the most effective approach. Start with a 30-day pilot program focusing on high-risk documents. Between days 30 and 60, expand the program to include medium-risk processes while tracking key performance indicators (KPIs). By day 90, fine-tune verification thresholds and incorporate advanced tools like Public Key Infrastructure (PKI) for high-value transactions. For instance, a mid-size business that reduces its contract dispute rate by 30% on $5 million worth of annual agreements can often justify the investment in document verification and PKI within a year. These steps align with a broader risk-based strategy, ensuring consistent and effective global verification.
Collaborating with Technology Partners
Strong partnerships with the right technology providers can streamline verification across international borders. Look for providers offering flexible, document-agnostic systems that recognize more than 12,000 global ID types in over 48 languages – without requiring separate workflows for each country. This adaptability is crucial, especially when fraudsters are involved in about 1 out of every 25 online identity verification attempts.
Modern platforms integrate multiple verification tools – document checks, biometrics, device intelligence, and behavioral analysis – into a single, cohesive workflow. These systems go beyond simple pass/fail evaluations, using risk-based scoring to automatically approve low-risk users while flagging edge cases for manual review. Additionally, global compliance expertise is vital. Your technology partner should support regional data protection laws like GDPR, enforce data residency requirements, and prioritize localized consent management. Verification efforts shouldn’t stop after onboarding; continuous monitoring can help detect account takeovers or evolving fraud tactics.
When integrating these systems, consider whether to use SDKs for quick mobile and browser-based capture or APIs for more customized server-side workflows. In many global markets, mobile devices dominate, so verification processes must be camera-friendly and user-friendly to reduce abandonment rates.
Training and Adoption Across Teams
Technology alone isn’t enough to safeguard your operations – your team needs to know how to use it effectively. From the outset, involve stakeholders from product, security, legal, and compliance teams to ensure the system meets both regulatory and operational requirements.
Equip frontline teams with the knowledge to recognize cross-border fraud indicators, such as mismatches between geolocated IP addresses and claimed residence or the use of obscure payment service providers. Provide human reviewers with detailed tools that display device data, similarity scores, and behavioral patterns – not just binary pass/fail results – so they can make informed decisions. Combining advanced technology with skilled human oversight ensures a robust verification process at every level.
To prepare for real-world scenarios, conduct tabletop exercises simulating cross-border fraud cases. These exercises should involve legal, compliance, payments, and investigation teams working together to respond effectively. Build feedback loops that allow human reviewers to correct automated decisions quickly, enabling the system to adapt to new fraud patterns. Scott Johnson, Vice President of Technical Program Management at Convera, highlights the importance of flexibility in this fast-evolving space:
"Businesses should certainly pay attention now, as this has the potential to move quite quickly. And so you should be ready, understand what digital wallets can and can’t do, pilot an experiment, be agile, and be willing to pivot".
How Accounts Receivable Insurance Supports Identity Verification
Accounts Receivable Insurance (ARI) goes a step beyond digital identity verification by addressing financial risks that identity checks alone can’t mitigate. While digital identity tools are effective at detecting fraudulent entities, they don’t shield businesses from payment defaults. ARI fills this gap by pairing verified identity data with tailored credit protection, creating a two-layer safeguard against fraud and financial loss in international trade. This dual protection ensures that receivables are secured throughout the often lengthy and unpredictable payment cycles of cross-border transactions.
ARI providers leverage digital identity data to evaluate the creditworthiness and legitimacy of international customers before issuing policies or setting credit limits. This approach allows for early risk detection and provides more favorable terms for verified, trustworthy partners.
Mitigating Non-Payment Risks
International trade often involves extended payment cycles, which can increase the risk of non-payment. ARI directly addresses this issue by covering up to 95% of outstanding receivables if a foreign buyer fails to pay. This protection applies to two key risk categories:
- Commercial risks: These include buyer insolvency or prolonged payment delays.
- Political risks: These encompass challenges such as war, currency restrictions, or government actions that prevent payment.
For example, even if a buyer in a politically unstable region clears identity verification, they could later declare bankruptcy. In such cases, ARI ensures that the insured receivables remain protected.
Modern ARI platforms integrate AI-powered tools into credit decision-making processes, enabling real-time risk monitoring and dynamic credit adjustments. Fraudsters, who are four times more likely to exploit stolen real identities rather than synthetic ones, can be detected more effectively by combining behavioral signals with traditional credit analysis. This enhanced monitoring helps identify suspicious activity, such as compromised identities being used for fraudulent transactions.
International payment cycles can stretch from 60 to 180 days, far longer than the typical domestic Net 30 terms. During this time, a buyer’s financial situation could deteriorate, or unforeseen political events might disrupt payments. ARI bridges this gap, protecting receivables from risks that emerge after identity verification but before payment is made.
Providing Risk Assessments for Cross-Border Trade
ARI providers tailor policies to address the unique political and economic risks of specific international markets. These customized policies rely on digital identity data to create baseline risk profiles for each trading relationship. Below are examples of how ARI policies address region-specific risks:
| Political Risk Component | Description of Coverage |
|---|---|
| Currency Inconvertibility | Protects against losses when a government restricts currency exchange or transfer |
| Expropriation | Covers losses from foreign government actions like nationalization or asset confiscation |
| Political Violence | Provides coverage for losses caused by war, civil unrest, or terrorism that disrupt payments |
| Breach of Contract | Safeguards against losses when a foreign government cancels a contract unilaterally |
Jordan Burris, Head of Public Sector at Socure, highlights the broader implications of these risks:
"Government agencies are under coordinated attack from nation states hellbent on exploiting weaknesses in existing identity infrastructure. This is a matter of national security".
Organized fraud rings, which account for up to 12% of applications for some government services and loans, also pose a significant threat to international trade. ARI providers incorporate intelligence about these risks into their assessments, adjusting coverage and premiums to reflect the threat landscape.
Additionally, businesses that utilize ARI are often viewed as lower risk by financial institutions. When lenders see that buyer identities are verified and receivables are insured, they are more likely to offer trade financing. This reduces barriers to accessing working capital and improves insurance terms, making ARI a valuable tool for businesses engaged in global trade.
Future Trends in Digital Identity Verification for Trade
The landscape of digital identity verification is evolving, bringing solutions that tackle scalability, ownership, and advanced risk detection in international trade.
The next wave of digital identity systems is poised to transform how businesses verify cross-border partners. Blockchain-based frameworks are no longer just experimental; they are finding practical applications. For example, the EU has mandated that all member states must provide a European Digital Identity Wallet to citizens by November 26, 2026. These wallets will allow businesses to share secure credentials without relying on centralized databases, streamlining international trade processes. As David Campos, Head of Partnerships at GLEIF, explains:
"The bottleneck inhibiting global digital is no longer the legal validity of electronic documents; it is the need for trusted digital interactions between organizations."
This shift is setting the stage for even more advancements.
Building on blockchain technology, Self-Sovereign Identity (SSI) is gaining traction. The market for SSI is projected to grow from $3 billion in 2024 to $39 billion by 2033. This decentralized approach gives businesses full control over their verification data, enabling selective sharing of credentials while safeguarding sensitive information. By late 2025, 42% of business leaders had already begun integrating digital IDs into their systems, with 75% predicting better customer experiences and 71% expecting stronger fraud prevention measures.
Artificial intelligence is also stepping up to counter increasingly sophisticated fraud tactics. In one notable case from 2024, fraudsters used deepfake technology to impersonate a company’s CFO during a video conference, leading to a $25 million wire transfer. Modern fraud detection platforms now analyze over 1,000 risk signals, including device telemetry, behavioral biometrics, and transaction contexts, going far beyond traditional document checks. This new level of analysis highlights the growing need for advanced tools to identify risks.
On a global scale, regulatory alignment is paving the way for seamless cross-border digital identity recognition. Frameworks like the UNCITRAL Model Law on Identity Management and Trust Services, adopted in July 2022, are helping to standardize these efforts. In the UK, the Digital Identity and Attributes Trust Framework, now supported by the Data (Use and Access) Act 2025, adheres to ISO and W3C standards, ensuring compatibility with other national systems. These initiatives reduce the compliance burden for businesses navigating international trade.
Privacy-preserving technologies, such as Zero-Knowledge Proofs, are also gaining momentum. These tools allow verifiers to confirm specific attributes – like whether an entity is authorized for trade – without accessing sensitive underlying data. This approach is particularly important given that nearly 1 billion people globally lack government-recognized ID. Emerging models are blending state oversight for legal legitimacy with decentralized verification layers, balancing security and compliance while protecting individual data.
Together, these advancements are shaping a stronger, more secure digital verification ecosystem that supports businesses in managing cross-border transactions effectively.
Conclusion
Digital identity verification plays a key role in securing international trade. By using layered authentication – such as document verification, biometric checks, device intelligence, and behavioral analysis – companies can build a strong defense against increasingly sophisticated threats like synthetic identity fraud and deepfake impersonation. This approach not only protects identities but also supports stable financial operations.
The financial stakes are high. With the immense volume of cross-border payments, businesses that automate KYC (Know Your Customer) and KYB (Know Your Business) processes can keep pace with real-time payment systems while ensuring compliance across various jurisdictions.
Even with advanced verification tools, some risks remain – and that’s where Accounts Receivable Insurance (ARI) steps in. While digital identity verification confirms who your trading partner is, ARI safeguards against financial losses from events like bankruptcies, political instability, or payment defaults. Together, these solutions form a two-layered approach: verification prevents fraud from entering your system, and insurance shields you from commercial risks that pass initial checks. This dual strategy creates a comprehensive risk management framework, as outlined in this guide.
For companies venturing into international markets, this combined approach shifts risk management from being merely reactive to a strategic advantage. Businesses can seize cross-border opportunities with greater confidence, supported by secure verification processes and financial protection. With 71% of business leaders anticipating better security from digital ID integration, and the self-sovereign identity market forecasted to grow from $3 billion in 2024 to $39 billion by 2033, the tools for safer global trade are advancing quickly.
To move forward, businesses must adopt risk-based verification strategies, identify vulnerabilities in cross-border interactions, and align their digital identity systems with insurance coverage. These steps empower companies to thrive in the global marketplace while safeguarding their operations and financial health.
FAQs
What’s the best verification stack for high-value international trade deals?
When it comes to high-value international trade, ensuring trust and security is non-negotiable. The ideal verification stack blends cutting-edge technology with global standards to authenticate parties seamlessly across borders.
Key elements include biometric verification, AI-powered tools, and digital profiles. These technologies work together to confirm identities with precision, even in complex cross-border environments. Standards like the Legal Entity Identifier (LEI) and its enhanced version, the verifiable LEI (vLEI), play a pivotal role in building trust. They enable secure, paperless transactions while reducing the risk of fraud and ensuring compliance with international regulations.
This combination of advanced tools and globally recognized standards provides a robust framework for managing the challenges of international trade.
How do LEI and vLEI reduce B2B trade fraud in practice?
Legal Entity Identifiers (LEIs) and verifiable LEIs (vLEIs) play a key role in combating B2B trade fraud by offering a reliable method for organizations to confirm their identity during digital transactions. LEIs are unique 20-character codes that help prevent identity impersonation, while vLEIs take it a step further by incorporating cryptographic proof, ensuring tamper-proof authentication. Together, these tools enhance the security of cross-border interactions, minimize fraud risks, and simplify compliance by providing reusable, verified digital identities.
How does Accounts Receivable Insurance work with identity verification to cover non-payment risk?
Accounts Receivable Insurance (ARI) works hand-in-hand with digital identity verification to tackle non-payment risks in international trade. By using identity verification, businesses can confirm a buyer’s legitimacy and assess their financial stability, reducing the chances of fraud or misrepresentation. ARI steps in to cover the remaining risks, such as insolvency, fraud, or political disruptions, offering protection even when unexpected non-payment arises. Together, these tools create a strong safety net for cross-border transactions.



